نرم افزار VMware NSX محصولی از سوی شرکت VMware برای مجازی سازی شبکه های فیزیکی است.
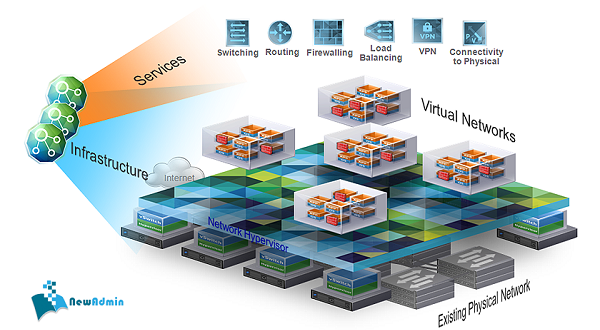
شرکت VMware با صرف هزینه یک میلیارد دلاری این پروژه را از شرکت Nicira تصاحب کرد. طبق تعریف این شرکت، نرم افزار NSX همان ESX برای شبکه است. این تعریف برای درک بهتر مطرح شده است چرا که بیشتر ما می دانیم در واقع VMware ESXi منابع رایانش یا همان سرور فیزیکی را مجازی سازی می کند. (مثل CPU ،Memory ،Hard disk و کارت های شبکه). در مقایسه با آن VMware NSX کل شبکه زیرساخت آن را مجازی سازی می کند. (مثل switch مجازی، firewall مجازی، router مجازی، Load Balancer مجازی و …)
دو نسخه مختلف از NSX وجود دارد:
- NSX برای vSphere
- NSX برای Multi-Hypervisor (یا به اختصار MH)
NSX برای vSphare، محصولی ایده آل برای محیط های VMware محسوب می شود، در حالی که NSX برای MH به منظور یکپارچه سازی محیط های Cloud طراحی شده است و استانداردهای مختلفی از جمله OpenStack را به کار می گیرد.
از ویژگی های بارز این بسته نرم افزاری می توان به موارد زیر اشاره کرد:
- عدم وابستگی شبکه به سخت افزار.
- منعطف سازی شبکه، می توانید شبکه ای را که نیاز دارید در لحظه (بسازید، پاک کنید، و آن را ویرایش کنید).
- شفاف نمودن شبکه برای نرم افزار ها.
- قابلیت نظارت برنامه ریزی شده.
- فراهم آوری زیرساخت قابل توسعه شبکه و استفاده از نرم افزار های جانبی (Third-party) به عنوان راه کار های مورد نیاز.
?باتوجه قولی که یکی ازدوستان مادرکشور اوکراین به مادادند،انشالله درهفته دوم سپتامبر سال جاری میلادی ؛ امکان دانلود نسخه VMware-NSX-Manager-6.2.4-4292526 فراهم خواهد شد. ⁉️
دانلود VMware NSX 6.2.3
![]()
Pass : newadmin.ir
در زیر امکانات جدید فراهم شده در نسخه 6.2.3 به نقل از سایت Vmware نقل شده است:
- The 6.2.3 release delivers a security patch CVE-2016-2079 which is a critical input validation vulnerability for sites that uses NSX SSL VPN. It also includes a number of bug fixes documented in the Resolved Issues section.
- Logical Switching and Routing
- NSX Hardware Layer 2 Gateway Integration: expands physical connectivity options by integrating 3rd-party hardware gateway switches into the NSX logical network.
- New VXLAN Port 4789 in NSX 6.2.3 and later: Before version 6.2.3, the default VXLAN UDP port number was 8472. See the NSX Upgrade Guide for details.
- Networking and Edge Services
- New Edge DHCP Options: DHCP Option 121 supports static route option, which is used for DHCP server to publish static routes to DHCP client; DHCP Options 66, 67, 150 supports DHCP options for PXE Boot; and DHCP Option 26 supports configuration of DHCP client network interface MTU by DHCP server.
- Increase in DHCP Pool, static binding limits: The following are the new limit numbers for various form factors: Compact: 2048; Large: 4096; Quad large: 4096; and X-large: 8192.
- Edge Firewall adds SYN flood protection: Avoid service disruptions by enabling SYN flood protection for transit traffic. Feature is disabled by default, use the NSX REST API to enable it.
- NSX Edge — On Demand Failover: Enables users to initiate on-demand failover when needed.
- Change in NSX Edge Upgrade Behavior: Replacement NSX Edge VMs are deployed before upgrade or redeploy. The host must have sufficient resources for four NSX Edge VMs during the upgrade or redeploy of an Edge HA pair. Default value for TCP connection timeout is changed to 21600 seconds from the previous value of 3600 seconds.
- Cross VC NSX — Universal Distributed Logical Router (DLR) Upgrade: Auto upgrade of Universal DLR on secondary NSX Manager, once upgraded on primary NSX Manager.
- Flexible SNAT / DNAT rule creation: vnicId no longer needed as an input parameter; removed requirement that the DNAT address must be the address of an NSX Edge VNIC.
- NSX Edge VM (ESG, DLR) now shows both Live Location and Desired Location. NSX Manager and NSX APIs including GET api/4.0/edges//appliances now return configuredResourcePool and configuredDataStore in addition to current location.
- Edge Firewall adds SYN flood protection: Avoid service disruptions by enabling SYN flood protection for transit traffic. Feature is disabled by default, use the NSX REST API to enable it.
- NSX Manager exposes the ESXi hostname on which the 3rd-party VM Series firewall SVM is running to improve operational manageability in large-scale environments.
- NAT rule now can be applied to a VNIC interface and not only an IP address.
- New configuration option to set the load balancer session aging time: This release delivers a new application rule command to set the session aging timeout value for both the server and client. If the pool is shared among multiple virtual servers, the maximum value will be set for it.
- Security Services
- Distributed Firewall — TFTP ALG: Enables use cases such as network boot for VMs.
- Firewall — Granular Rule Filtering: Simplifies troubleshooting by providing granular rule filters in UI, based on Source, Destination, Action, Enabled/Disabled, Logging, Name, Comments, Rule ID, Tag, Service, Protocol.
- Guest Introspection — Windows 10 support
- SSL VPN Client — Mac OS El Capitan support
- Service Composer — Performance Improvements: Enables faster startup/reboot of NSX Manager by optimizing synchronization between security policy and firewall service, and disabling auto-save of firewall drafts by default.
- Service Composer — Status Alarms: Raises system alarm if security policy is out-of-sync, and takes specific actions based on alarm code to resolve issue.
- Reduction in firewall heap memory usage: Firewall usage of IP address sets has been optimized to reduce heap memory usage.
- Operations and Troubleshooting
- NSX Dashboard: Simplifies troubleshooting by providing visibility into the overall health of NSX components in one central view.
- Traceflow Enhancement — Network Introspection Services: Enhances ability to trace a packet from source to destination, by identifying whether packets were forwarded to 3rd-party network introspection services, and whether the packet comes back from the 3rd-party service VM or not.
- SNMP Support: Configure SNMP traps for events from NSX Manager, NSX Controller, and Edge.
- Logging is now enabled by default for SSL VPN and L2 VPN. The default log level is notice.
- Logging for IPsec VPN is now enabled by default Default log level is set to warning. If you wish to disable logging or change the log level, see the section, “Enable Logging for IPSec VPN” in the NSX Administration Guide.
- Firewall rules UI now displays configured IP protocols and TCP/UDP port numbers associated with services.
- NSX Edge technical support logs have been enhanced to report memory consumption per process.
- Enhanced communication channel health status monitoring with new event log messages reported when the channel health status changes for a server or a cluster.
- Central CLI Enhancements
- Central CLI for Host Health: Shows host health status, with 30+ checks in one command (including network config, VXLAN config, resource utilization, etc.)
- Central CLI for Packet Capture: Provides ability to capture packet on the host and transfer the capture file to user’s remote server. This eliminates the need to open up hypervisor access to network administrators, when troubleshooting logical network issues.
- Technical support bundle per host: Gathers per-host logs and creates a bundle that can be saved and submitted to VMware technical support for assistance.
- Licensing Enhancements
- Change in default license & evaluation key distribution: default license upon install is “NSX for vShield Endpoint”, which enables use of NSX for deploying and managing vShield Endpoint for anti-virus offload capability only. Evaluation license keys can be requested through VMware sales.
- License usage reporting: NSX license usage counts are displayed on NSX Manager’s Summary UI and also retrievable via API. NSX license usage counts will no longer be reported through vCenter licensing service.
- Load Balancer (LB) Enhancements
- Configurable session timeout for VIP configured without acceleration: Ability to configure Load Balancing L7 engine (no acceleration) VIP timeout above 5 minutes using the Application Rule “timeout client 3600s”.
- Statistics enhancement on CLI: Global statistics are now available through CLI. Specific VIP and pool statistics are also available.
- LB with acceleration enhancement : Load Balancing L4 engine (acceleration enabled) will now always honor the health checks UDP, TCP source IP hash, and invalidate persistent entry.
- Log refinements: Load Balancer log improvements.
- Configurable SSL authentication: Ability to configure SSL server authentication in case of VIP with end-to-end SSL.
- Source IP Persistent table enhancement: Even after a configuration change, the Source IP Persistence table remains available.
- NSX Edge load balancer system control (sysctl) sysctl.net.ipv4.vs.expire_nodest_conn parameter added to NSX Manager whitelist: The sysctl.net.ipv4.vs.expire_nodest_conn to change the persistent connection status.
- Solution Interoperability
- Customer Experience Improvement Program: NSX supports reporting system statistics via the VMware Customer Experience Improvement Program (CEIP). Participation is optional and is configured in the vSphere Web Client.
- VMware vRealize Log Insight 3.3.2 for NSX provides intelligent log analytics for NSX, with monitoring and troubleshooting capabilities and customizable dashboards for network virtualization, flow analysis and alerts. This version accepts NSX Standard/Advanced/Enterprise edition license keys issued for NSX 6.2.2+.
- vShield Endpoint Management Support: NSX supports management of vShield Endpoint anti-virus offload capabilitie. Customers who purchased vSphere with vShield Endpoint (Essentials Plus and above) can download NSX from the vSphere download site. For more information, refer to VMware knowledge base article 2110078 and VMware knowledge base article 2105558.




Can you please password for zip file